By
Brian Krebs
AshleyMadison.com, a site that helps married people
cheat and whose slogan is “Life is Short, have an Affair,” recently put
up a half million (Canadian) dollar bounty for information leading to
the arrest and prosecution of the
Impact Team — the name chosen by the hacker(s) who recently
leaked data
on more than 30 million Ashley Madison users. Here is the first of
likely several posts examining individuals who appear to be closely
connected to this attack.
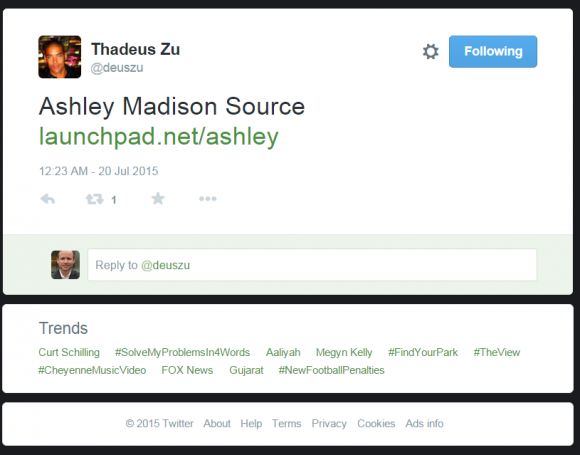
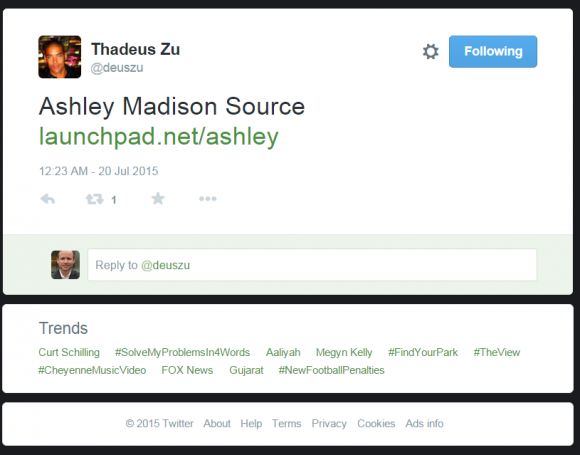
It was just past midnight on July 20, a few hours after I’d
published an exclusive story
about hackers breaking into AshleyMadison.com. I was getting ready to
turn in for the evening when I spotted a re-tweet from a Twitter user
named
Thadeus Zu (@deuszu) who’d just
posted a link to the same cache of data
that had been confidentially shared with me by the Impact Team via the
contact form on my site just hours earlier: It was a link to the
proprietary source code for Ashley Madison’s service.
Initially, that tweet startled me because I couldn’t find any other
sites online that were actually linking to that source code cache. I
began looking through his past tweets and noticed some interesting
messages, but soon enough other news events took precedence and I forgot
about the tweet.
I revisited Zu’s tweet stream again this week after watching a press conference held by the Toronto Police (where
Avid Life Media,
the parent company of Ashley Madison, is based). The Toronto cops
mostly recapped the timeline of known events in the hack, but they did
add one new wrinkle: They said Avid Life employees first learned about
the breach on July 12 (seven days before my initial story) when they
came into work, turned on their computers and saw a threatening message
from the Impact Team accompanied by the anthem “
Thunderstruck” by Australian rock band AC/DC playing in the background.
After
writing up a piece on the bounty offer,
I went back and downloaded all five years’ worth of tweets from Thadeus
Zu, a massively prolific Twitter user who typically tweets hundreds if
not thousands of messages per month. Zu’s early years on Twitter are a
catalog of simple hacks — commandeering unsecured routers, wireless
cameras and printers — as well as many, many Web site defacements.
On the defacement front, Zu focused heavily on government Web sites
in Asia, Europe and the United States, and in several cases even taunted
his targets. On Aug. 4, 2012,
he tweeted to KPN-CERT, a computer security incident response team in the Netherlands, to alert the group that he’d hacked their site. “
Next time, it will be Thunderstruck. #ACDC” Zu wrote.
The day before, he’d compromised the Web site for the Australian Parliament, taunting lawmakers there with
the tweet: “
Parliament of Australia bit.ly/NPQdsP Oi! Oi! Oi!….T.N.T. Dynamite! Listen to ACDC here.”
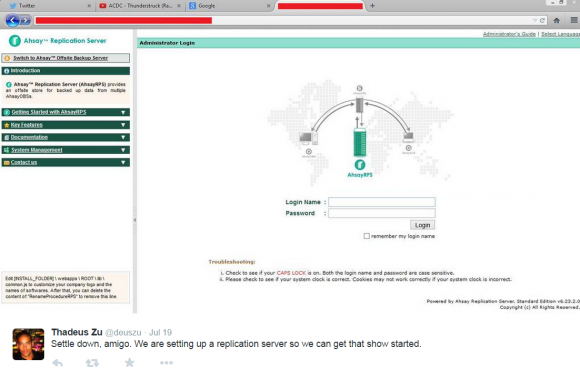
I began to get very curious about whether there were any signs on or
before July 19, 2015 that Zu was tweeting about ACDC in relation to the
Ashley Madison hack. Sure enough: At
9:40 a.m., July 19, 2015
— nearly 12 hours before I would first be contacted by the Impact Team —
we can see Zu is feverishly tweeting to several people about setting up
“
replication servers” to “
get the show started.” Can you spot what’s interesting in the tabs on his browser in the screenshot he tweeted that morning?
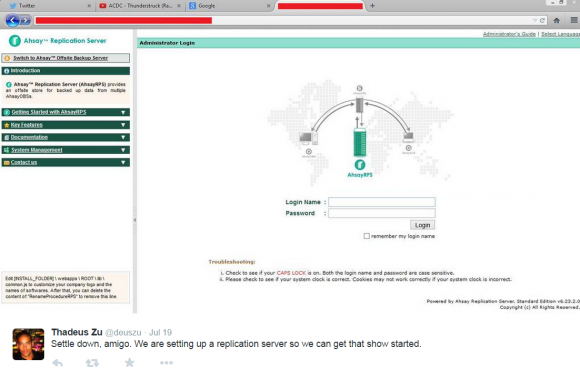
Twitter
user ThadeusZu tweets about setting up replication servers. Did you
spot the Youtube video he’s playing when he took this screenshot?
Ten points if you noticed the Youtube.com tab showing that he’s listening to AC/DC’s “Thunderstruck.”
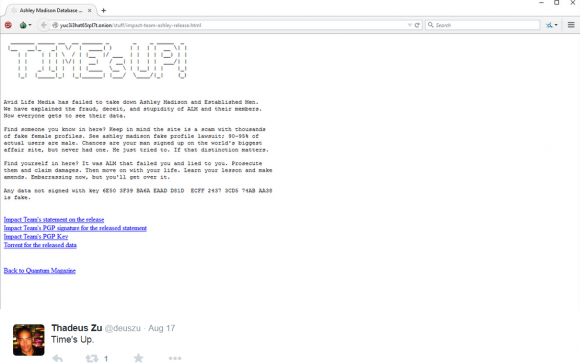
A week ago, the news media pounced on the Ashley Madison story once
again, roughly 24 hours after the hackers made good on their threat to
release the Ashley Madison user database. I went back and examined Zu’s
tweet stream around that time and found he beat
Wired.com,
ArsTechnica.com and every other news media outlet by more than 24 hours with the Aug. 17 tweet, “
Times up,”
which linked to the Impact Team’s now infamous post listing the sites
where anyone could download the stolen Ashley Madison user database.
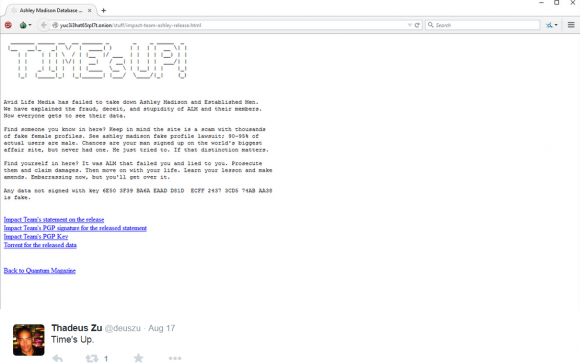
ThadeusZu tweeted about the downloadable Ashley Madison data more than 24 hours before news outlets picked up on the cache.
WHO IS THADEUS ZU?
As with the social networking profiles of others who’ve been tied to
high-profile cybercrimes, Zu’s online utterings appear to be filled with
kernels of truth surrounded by complete malarkey– thus making it
challenging to separate fact from fiction. Hence, all of this could be
just one big joke by Zu and his buddies. In any case, here are a few key
observations about the who, what and where of Thadeus Zu based on
information he’s provided (again, take that for what it’s worth).
Zu’s Facebook profile
wants visitors to think he lives in Hawaii; indeed, the time zone set
on several of his social media counts is the same as Hawaii. There are a
few third-party Facebook accounts of people demonstrably living in
Hawaii who tag him in their personal photos of events on Hawaii (see
this cached photo,
for example), but for the most part Zu’s Facebook account consists of
pictures taken from stock image collections and do not appear to be
personal photos of any kind.
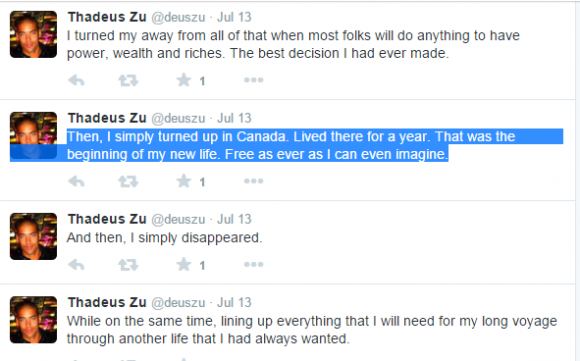
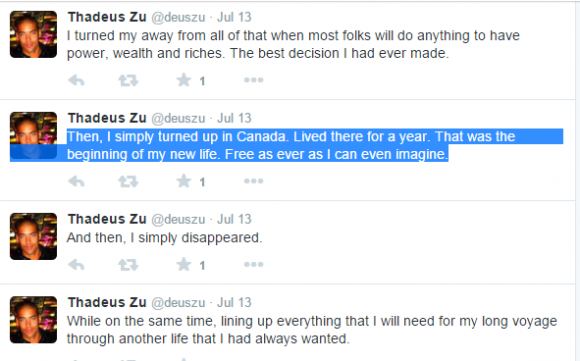
A few tweets from Zu — if truthful and not simply premeditated
misdirection — indicate that he lived in Canada for at least a year,
although it’s unclear when this visit occurred.
Zu’s
various Twitter and Facebook pictures all feature hulking, athletic,
and apparently black male models (e.g. he’s appropriated two profile
photos of male model
Rob Evans).
But Zu’s real-life identity remains murky at best. The lone exception I
found was an image that appears to be a genuine group photo taken of a
Facebook user tagged as Thadeus Zu, along with an unnamed man posing in
front of a tattoo store with popular Australian (and very
inked) model/nightclub DJ
Ruby Rose.
That photo is no longer listed in Rose’s Facebook profile, but a cached version of it is available
here.
Rose’s tour schedule indicates that she was in New York City when that
photo was taken, or at least posted, on Feb. 6, 2014. Zu is tagged in
another Ruby Rose Facebook post five days later on Valentine’s Day.
Update, 2:56 p.m.:
As several readers have pointed out, the two people beside Rose in
that cached photo appear to be Franz Dremah and Kick Gurry, co-stars in
the movie
Edge of Tomorrow).
Other clues in his tweet stream and social media accounts put Zu in Australia. Zu has a Twitter account under the Twitter nick
@ThadeusZu, which has a whopping 11 tweets, but seems rather to have been used as a news feed. In that account Zu
is following some 35 Twitter accounts,
and the majority of them are various Australian news organizations.
That account also is following several Australian lawmakers that govern
states in south Australia.
Then again, Twitter auto-suggests popular accounts for new users to
follow, and usually does so in part based on the Internet address of the
user. As such, @ThadeusZu may have only been using an Australian Web
proxy or a
Tor node
in Australia when he set up that account (several of his self-published
screen shots indicate that he regularly uses Tor to obfuscate his
Internet address).
Even so, many of Zu’s tweets going back several years place him in
Australia as well, although this may also be intentional misdirection.
He continuously
references his “Oz girl,” (“Oz” is
another word for Australia) uses the greeting “cheers” quite a bit, and even talks about people visiting him in Oz.
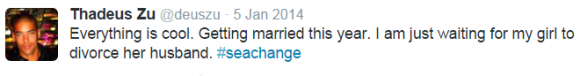
Interestingly, for someone apparently so caught up in exposing
hypocrisy and so close to the Ashley Madison hack, Zu appears to have
himself courted a married woman — at least according to his own tweets.
On January 5, 2014, Zu tweeted:
“Everything is cool. Getting married this year. I am just waiting for my girl to divorce her husband. #seachange
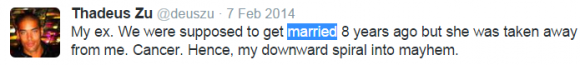
A month later, on Feb. 7, 2014, Zu offered this tidbit of info:
“My ex. We were supposed to get married 8 years ago but she was taken
away from me. Cancer. Hence, my downward spiral into mayhem.”
To say that Zu tweets to others is a bit of a misstatement. I have
never seen anyone tweet the way Zu does; He sends hundreds of tweets
each day, and while most of them appear to be directed at nobody, it
does seem that they are in response to (if not in “reply” to) tweets
that others have sent him or made about his work. Consequently, his
tweet stream appears to the casual observer to be nothing more than an
endless soliloquy.
But there may something else going on here. It is possible that Zu’s
approach to tweeting — that is, responding to or addressing other
Twitter users without invoking the intended recipient’s Twitter handle —
is something of a security precaution. After all, he had to know and
even expect that security researchers would try to reconstruct his
conversations after the fact. But this is far more difficult to do when
the Twitter user in question never actually participates in threaded
conversations.
People who engage in this way of tweeting also do not
readily reveal the Twitter identities of the people with whom they chat
most.
Thadeus Zu — whoever and wherever he is in real life — may not have
been directly involved in the Ashley Madison hack; he claims in several
tweets that he was not part of the hack, but then in countless tweets he
uses the royal “We” when discussing the actions and motivations of the
Impact Team. I attempted to engage Zu in private conversations without
success; he has yet to respond to my invitations.
It is possible that Zu is instead a white hat security researcher or
confidential informant who has infiltrated the Impact Team and is merely
riding on their coattails or acting as their mouthpiece. But one thing
is clear: If Zu wasn’t involved in the hack, he almost certainly knows
who was.
KrebsOnSecurity is grateful to several researchers, including
Nick Weaver,
for their assistance and time spent indexing, mining and making sense
of tweets and social media accounts mentioned in this post. Others who
helped have asked to remain anonymous. Weaver has published some
additional thoughts on this post
over at Medium.